Note: ALL TEAMS ARE REQUIRED TO HAVE 64-BIT, HOST COMPUTERS AND OPERATING SYSTEM TO COMPETE SUCCESSFULLY IN CYBERPATRIOT.
Cisco Training Materials and Networking Academy Enrollment will be available in September.
Each competition round has two challenges for which teams will need to train.
- Network Security Challenge (Operating System Images)
- Cisco Networking Challenge (Quiz and Packet Tracer)
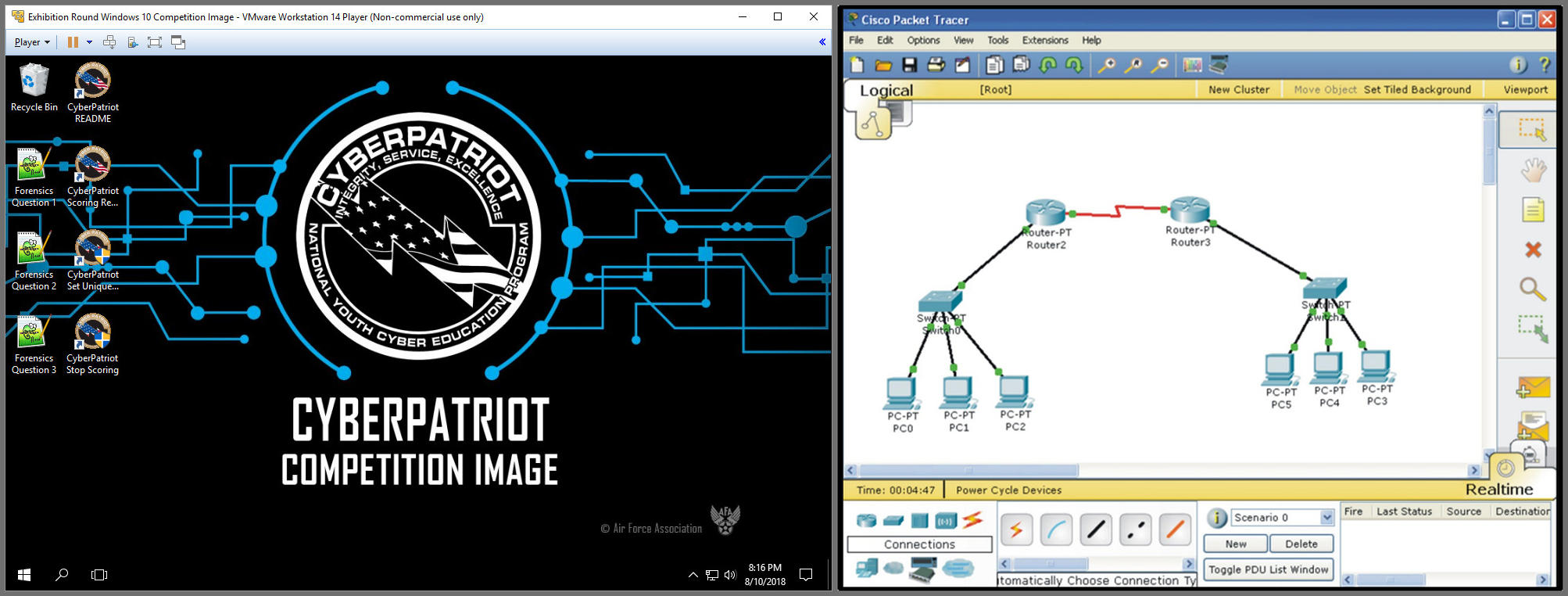
Competition Image Packet Tracer
Self Paced Cisco NetAcad Linux and Networking Courses
The courses below are offered by our sponsor, Cisco.
To access courses, please see New Coach Resources under the Competition Tab on the CyberPatriot website
Education for Everyone!
These two courses will benefit you in your day-to-day life.
- Get Connected:
- Introduction to Cybersecurity:
Explore IT (Information Technology)!
If you want to take your initial tech skills to the next level, these courses will help you do that.
- Cybersecurity Essentials:
- Introduction to IoT:
- Introduction to Packet Tracer:
- NDG Linux Unhatched:
Pave the Way for New Skills!
Interested in preparing yourself for a new career path? These courses will help you do that!
- NDG Linux Essentials:
- PCAP: Programming Essentials in Python:
- Networking Essentials:
Career Building Opportunity!
This workshop offers advice on navigating the hiring process and maximizing tools available.
- Talent Bridge Career Preparation:
** Helpful tips: The
recommended browsers are Firefox or Chrome. To launch the End of Course
Feedback Survey and the Final Exam in all courses, you will need to enable pop-up windows. If you have any issues logging in, please clear the cache &
cookies and close the browser completely. Then, re-launch the browser and log back
in.
Network Security Challenge (Images)
The main goal of every round of competition is to improve the security of one or more virtual machine images. In the past, teams have been tasked with:
- Maintaining and hardening critical services
- Fixing vulnerabilities
- Removing malware from the systems
- Answering forensics questions
In the past, CyberPatriot has used these images during the online rounds:
- Windows 10, Windows 11
- Windows Server 2019, Server 2022
- Ubuntu 22, Mint 21
Teams do not need to have any of these specific operating systems installed directly on their computers. Rather, these images are played using VMware Workstation Pro software. More information on the technical requirements for using this free software can be found on the Technical Specifications page.
Training for the competition, in addition to the training materials, is provided in three UNSCORED rounds:
- Exhibition Round(s) - Unscored images for Recruiting and Training
- Training Round - Answer keys provided with images for guided training
- Practice Round - Unscored images for team practice
For help playing a virtual machine image and beginning a competition round, please view this instructional video:
https://youtu.be/4UveDN7xn9I
Cisco Networking Challenge (Quiz and Packet Tracer Exercise)
Teams access the Cisco Networking Challenge through the Networking Academy website at
www.netacad.com. Teams will use two main courses:
- Content Course (Training)
- Competition Course (Competition Round Quiz and Packet Tracer Exercise)
All Quizzes and Packet Tracer exercises will be based on assigned training materials in the Content Course. Packet Tracer is a network simulator in which the students create virtual networks. The content (Training) course is normally available in September of the competition season.
Teams start with basic networking and security concepts and more advanced concepts are added as teams progress in the competition training. In previous seasons, teams have been given networking challenges, such as:
- Virtual Network Configuration
- Subnetting and IP Addressing
- Wireless Routing
The training pages in the menu to the left are intended to provide teams with basic cybersecurity knowledge. However, it is not an exhaustive list and may be insufficient for the more challenging rounds of competition. After reviewing these materials, teams should delve deeper into each of the presented topics and look to their Coaches and Mentors for further training. If you have a link that you think would be helpful for training, please send us an email at cpoc@uscyberpatriot.org.